Recently, there has been a lot of buzz around password security. Every week, security decision-makers are inundated with advice like “never use a compromised password”, “always choose really long passwords” and the popular notion that “passphrases will save us.” But according to research that Microsoft has done, combined with the daily reality of defending against hundreds of millions of password-based attacks, suggests that an excessive focus on password rules is just a distraction. The real game-changers are multi-factor authentication (MFA) and effective threat detection.
Despite the hype, when it comes to composition and length, your password generally doesn’t matter. At the heart of the matter is the attacker’s main goal, which is to steal passwords to gain unauthorized access. It is crucial to distinguish between hypothetical and practical security. Attackers will only go to extremes when there are no easier options, and the goal justifies the effort.
Password Spray Attacks
A primary method used by attackers is the “Password Spray” tactic. Here, attackers use easily accessible user lists to guess passwords across a large number of usernames. They ensure they work at a pace and spread their attempts across different IP addresses to avoid detection. Tools for this method are readily available and inexpensive.
In recent cases, it has been observed that during a spray attack, most attackers try about 10 passwords. But the beauty of a password spray is its detectability. Once detected, it can be stopped. Therefore, attackers take a “low and slow” approach, making every password guess crucial. They use information from previous leaks to create their attacks.
If your password is not on the attacker’s list, you are safe. Most attackers use similar lists and try the same passwords. Some examples include “123456”, “password” and “qwerty123”.
Database extraction and its consequences
A less common but crucial consideration is the threat of database extraction. The extraction process involves removing a domain controller’s files or accessing the Azure Active Directory cloud environment. The latter requires more effort, requires access to the environment, database decryption capabilities and, in some cases, Bitlocker key-breaking abilities.
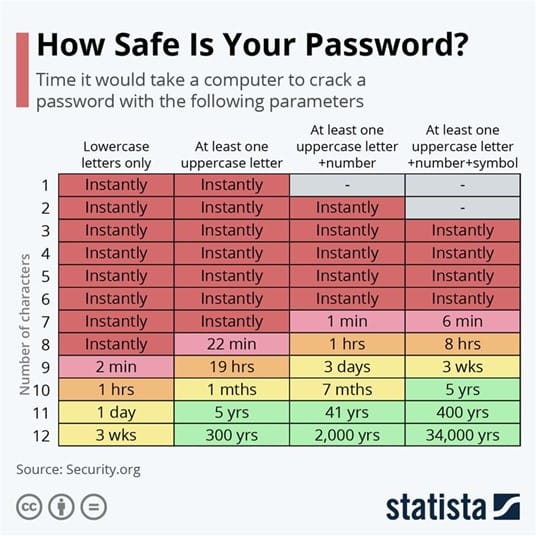
But once attackers have secured a database full of hashes, their next move is to get a cracking rig. With advances and reduced costs, powerful rigs are now available to experienced criminals. The password cracking process involves, in brief:
– Find out the rules for algorithms, salting and passwords.
– Create a list of potential passwords
– Trying all passwords against the target account
– Resorting to popular phrases, song lyrics or other common phrases
– Brute forcing, which quickly becomes tedious and time-consuming as password length increases
– Salting, in this case, ensures that each account’s password must be cracked individually
– The take-away, here, is that your password, in case of a breach, hardly matters, if it does not exceed 12 characters and is completely unique
Password Managers and MFA: The True Saviors
In contrast to traditional password performances, password managers can make a significant difference by generating long, random strings. While they come with their challenges, they offer a defense against brute-force attacks.
Yet the most potent defense is multi-factor authentication. MFA significantly reduces the chances of account compromise. With technological advances leading to better phishing techniques and more robust cracking rigs, it is clear that the future lies in cryptographically secure credentials attached to client hardware.
The overall theme here is that while your password may not matter as much as previously thought, MFA does. MFA reduces the probability of compromise by more than 99.9%. As technology advances, we must turn to more secure credentials, such as FIDO2, to ensure that we do not rely solely on passwords.